Securing Veeam Hardened Repository
- Get link
- X
- Other Apps
After selecting the right hardware for the Veeam Backup & Replication Hardened Repository and installing the Ubuntu Linux operating system, the next step is secure the operating system according to the DISA STIG (Defense Information Systems Agency Security Technical Implementation Guides) guidelines.
This blog post describes the hardening process for Ubuntu 20.04 free edition. For Ubuntu Pro users, there is an easier way. To keep it as simple as possible, Veeam provides a script that automates the setting of security options. The requirement for the script to work is such that Ubuntu is set up as described in the installing the Ubuntu Linux blog post.
Prerequisites
Before starting the hardening process, let’s recap the current state and adjust settings if needed.
- Hardware monitoring is enabled in the out-of-band management of the Hardened Repository server. Vendor-specific hardware monitoring tools are not covered in this blog post
- Minimal Ubuntu installation on an UEFI Secure boot-enabled physical system (virtual machines are unsupported/only for test installations)
- There is only one user account with full sudo permissions, and the root account is locked (no password)
- UDP port 123 outgoing is open on the firewall to the following servers (servers can be changed if needed. More details on NTP are available in this blog post and will be covered later in this article)
- tick.usno.navy.mil
- tock.usno.navy.mil
- ntp2.usno.navy.mil
That’s it! Let’s start securing Veeam Hardened Repository.
Getting started
After installing Ubuntu as described in this blog post, there are two ways to connect or manage the Veeam Hardened Repository.
- Direct login via the console (usually via a remote management console web interface)
- SSH (secure shell)
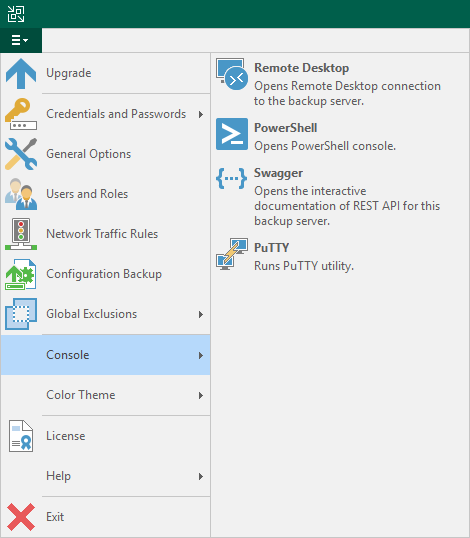
The easiest way is using SSH, because it supports copy and paste. One popular SSH client is Putty, which is included in the Veeam Backup & Replication installation.
Log in to the Hardened Repository server with your credentials (SSH or console). Then download the script with:
wget https://vee.am/harddisaBefore running the script, it’s recommended that you understand what it does and what it does not do. The script applies DISA STIG security settings where applicable. That means the script implements things like password policies, audit rules, permissions or TCP security settings. The STIGs also have requirements for systems with graphical user interface or user management via a directory service. As the Hardened Repository is a “minimal installation” standalone machine, things like that don’t apply and are “not applicable”. A full list of settings is available in the Appendix.
This guide assumes that customers reading this guide are new to Linux or have only basic Linux knowledge. The hardening script skips settings that have notifications where someone should do something manually on the Hardened Repository server as root. That is because the final and manual hardening step after the Veeam hardening script will remove root and sudo permissions and disable SSH remote management. This is a hard step, but it addresses concerns around “I can log in as root and delete files.”
For advanced Linux users: Feel free to use the script to save time. If you are using automation with Ansible, there is material available for that as well.
Apply DISA STIG Requirements
You can also apply each hardening step of the DISA STIGs manually. On the DISA document library, search for Ubuntu, download the guidelines and open them with DISA STIG Viewer. Most rules have a code example to apply the guideline.
The script in this article handles the rules of the guidelines to make your life easier. Before running the hardening script, one needs to make sure that NTP traffic is allowed to the servers listed in the script (tick.usno.navy.mil, tock.usno.navy.mil and ntp2.usno.navy.mil). Alternatively, one can change the script to other time sources, or configure time manually and delete the time configuration section in the script. Apply the guidelines by running the script with the following command:
sudo bash harddisaThe output will look like this. Explanations on all the steps are provided later in this document.
After the hardening script finished, the Veeam Hardened Repository role can be installed.
Install Hardened Repository Role
Technically, installing the Hardened Repository role could also be done before doing the hardening. Before adding the Hardened Repository role, you need to configure the filesystem path where the backup data will be stored in future. In the “Installing Ubuntu Linux for Veeam Hardened Repository” blog, we defined /mnt/backup as the path for backup data storage. This path needs to be owned by the Hardened Repository user and we will limit permissions only to that user (veeamrepo in our case):
sudo chown –R veeamrepo:veeamrepo /mnt/backup
sudo chmod 700
The user guide describes how to install the Veeam Hardened Repository role. Please note that the ‘use “su” if “sudo” fails’ option cannot be used because the root account has no password/is locked.
After installation of the Hardened Repository, there is still one user with full “sudo” privileges. Let’s close this.
Locking It Down
There are a few steps where we decided to keep it a manual process instead of automating it with the hardening script. One of them (others are described in the appendix table) is UBTU-20-010009, which states: “Ubuntu operating systems when booted must require authentication upon booting into single-user and maintenance modes.”Single-user mode is a way to get into the system after locking down Hardened Repository as described in the next section.
Protecting single-user mode against unauthorized access is described in a separate blog post.
These following steps are outside the official DISA STIG hardening guides. These steps are the answer to customer concerns about the security of Hardened Repository and the criticism that one can “simply” log in as root and delete everything.
First, we will disable SSH remote management. The following command disables the SSH service, so that it does not start automatically during boot time.
sudo systemctl disable sshYou can continue working with SSH until the next reboot. You can also stop the SSH service directly and the current SSH session will continue to work. But you can no longer reconnect after stopping the SSH service. The following command stops the SSH service:
sudo systemctl stop ssh The last commands above used “sudo” to give you root permissions. Root permissions are no longer needed to run Veeam Hardened Repository. We will only allow two commands: reboot and shutdown.
The overall concept of the following steps is also described in the Installing Ubuntu Linux for Veeam Hardened Repository blog post.
Replace the username with the username “veeamrepo” you are currently using:
sudo bash -c "echo 'veeamrepo ALL = (root) NOEXEC: /usr/sbin/reboot' >> /etc/sudoers"
sudo bash -c "echo 'veeamrepo ALL = (root) NOEXEC: /usr/sbin/shutdown' >> /etc/sudoers"
Now remove yourself from the sudo group. After executing the command below and next login, you lose your sudo permissions. To get full root/sudo permissions again, you must boot into “single-user mode”. Run this command only as last step!
sudo deluser veeamrepo sudoWith that, the configuration of the Hardened Repository itself is finished. But there are some more settings to become compliant with DISA STIGs.
Required Configurations on the Veeam Backup & Replication Side
There are DISA STIG requirements around encryption (see table below) that can be configured on the Hardened Repository directly or in Veeam Backup & Replication. The operating system data itself does not require protection. Only the backup data needs to be protected. One can protect the backup data also via disk encryption, but that increases complexity. It’s easier to manage encryption on the Veeam Backup & Replication side in the job settings.
| STIG ID | Severity | Rule title | Explanation |
| UBTU-20-010414 | medium | Ubuntu operating systems handling data requiring “data at rest” protections must employ cryptographic mechanisms to prevent unauthorized disclosure and modification of the information at rest. | Configure health checks and encryption in the job settings. Disk encryption could be used alternatively. |
| UBTU-20-010444 | medium | Ubuntu operating system must implement cryptographic mechanisms to prevent unauthorized modification of all information at rest. | Configure health checks in the job settings. Disk encryption could be used alternatively. |
| UBTU-20-010445 | medium | Ubuntu operating system must implement cryptographic mechanisms to prevent unauthorized disclosure of all information at rest. | Configure encryption in the job settings. Disk encryption could be used alternatively. |
Summary
As a “software only” vendor, Veeam offers customers flexibility regarding which hardware or operating system to use. On the other hand, customers ask for security best practices. Note the following blog series:
- Selecting Hardware and Setting Up Environment for Veeam Hardened Repository
- Installing Ubuntu Linux for Veeam Hardened Repository
- Securing Veeam Hardened Repository (this blog post)
With this blog series, customers are prepared to achieve trusted immutability by applying globally recognized DISA STIG cybersecurity standards on top of Veeam best practices. If you are looking for pre-configured immutable hardware, where you don’t need to manage the hardware and operating system yourself, then there are several options:
- Object storage with immutability support. There are around 30 partner solutions available today.
- As secondary target (remember the 3-2-1 Rule) you can use the HPE StoreOnce deduplication appliance with immutability.
- If tape is an option, then WORM tape media can ensure that data can never be deleted again (while with immutability, data can be deleted after the immutability retention is over).
- “Veeam Hardened Repository” as a service is offered by regional service providers (availability varies depending on location).
Appendix
The table below shows DISA STIG requirements that must be applied manually on the server hardware or in Veeam Backup & Replication.
| STIG ID | Severity | Rule title | Comment |
| UBTU-20-010009 | high | Ubuntu operating systems when booted must require authentication upon booting into single-user and maintenance modes. | Described above |
| UBTU-20-010012 | high | The Ubuntu operating system must ensure only users who need access to security functions are part of sudo group. | Described above |
| UBTU-20-010414 | medium | Ubuntu operating systems handling data requiring “data at rest” protections must employ cryptographic mechanisms to prevent unauthorized disclosure and modification of the information at rest. | Described above |
| UBTU-20-010444 | medium | Ubuntu operating system must implement cryptographic mechanisms to prevent unauthorized modification of all information at rest. | Described above |
| UBTU-20-010445 | medium | Ubuntu operating system must implement cryptographic mechanisms to prevent unauthorized disclosure of all information at rest. | Described above |
| UBTU-20-010447 | medium | The Ubuntu operating system must implement non-executable data to protect its memory from unauthorized code execution. | BIOS/UEFI setting |
| UBTU-20-010455 | medium | The Ubuntu operating system must disable all wireless network adapters. | Ensure that no wireless network adapters are used |
The table below shows the DISA STIG requirements that were implemented automatically by the script or are default settings.
| STIG ID | Severity | Rule Title | Comment |
|
UBTU-20-010005 |
medium |
The Ubuntu operating system must allow users to directly initiate a session lock for all connection types. |
|
|
UBTU-20-010007 |
low |
The Ubuntu operating system must enforce 24 hours/1 day as the minimum password lifetime. Passwords for new users must have a 24 hours/1 day minimum password lifetime restriction. |
|
|
UBTU-20-010008 |
low |
The Ubuntu operating system must enforce a 60-day maximum password lifetime restriction. Passwords for new users must have a 60-day maximum password lifetime restriction. |
|
|
UBTU-20-010013 |
medium |
The Ubuntu operating system must automatically terminate a user session after inactivity timeouts have expired. |
|
|
UBTU-20-010014 |
medium |
The Ubuntu operating system must require users to reauthenticate for privilege escalation or when changing roles. |
|
|
UBTU-20-010016 |
medium |
The Ubuntu operating system default filesystem permissions must be defined in such a way that all authenticated users can read and modify only their own files. |
|
|
UBTU-20-010035 |
medium |
The Ubuntu operating system must use strong authenticators in establishing nonlocal maintenance and diagnostic sessions. |
|
|
UBTU-20-010036 |
medium |
The Ubuntu operating system must immediately terminate all network connections associated with SSH traffic after a period of inactivity. |
|
|
UBTU-20-010037 |
medium |
The Ubuntu operating system must immediately terminate all network connections associated with SSH traffic at the end of the session or after 10 minutes of inactivity. |
|
|
UBTU-20-010038 |
medium |
The Ubuntu operating system must display the Standard Mandatory DoD Notice and Consent Banner before granting any local or remote connection to the system. |
Generic banner is used instead of DoD Notice. |
|
UBTU-20-010042 |
high |
The Ubuntu operating system must use SSH to protect the confidentiality and integrity of transmitted information. |
|
|
UBTU-20-010043 |
medium |
The Ubuntu operating system must configure the SSH daemon to use Message Authentication Codes (MACs) employing FIPS 140-2 approved cryptographic hashes to prevent the unauthorized disclosure of information and/or detect changes to information during transmission. |
|
|
UBTU-20-010047 |
high |
The Ubuntu operating system must not allow unattended or automatic login via SSH. |
|
|
UBTU-20-010048 |
high |
The Ubuntu operating system must be configured so that remote X connections are disabled, unless to fulfill documented and validated mission requirements. |
|
|
UBTU-20-010049 |
medium |
The Ubuntu operating system SSH daemon must prevent remote hosts from connecting to the proxy display. |
|
|
UBTU-20-010050 |
low |
The Ubuntu operating system must enforce password complexity by requiring that at least one upper-case character be used. |
|
|
UBTU-20-010051 |
low |
The Ubuntu operating system must enforce password complexity by requiring that at least one lower-case character be used. |
|
|
UBTU-20-010052 |
low |
The Ubuntu operating system must enforce password complexity by requiring that at least one numeric character be used. |
|
|
UBTU-20-010053 |
low |
The Ubuntu operating system must require the change of at least 8 characters when passwords are changed. |
|
|
UBTU-20-010054 |
medium |
The Ubuntu operating system must enforce a minimum 15-character password length. |
|
|
UBTU-20-010055 |
low |
The Ubuntu operating system must enforce password complexity by requiring that at least one special character be used. |
|
|
UBTU-20-010056 |
medium |
The Ubuntu operating system must prevent the use of dictionary words for passwords. |
|
|
UBTU-20-010057 |
medium |
The Ubuntu operating system must be configured so that when passwords are changed or new passwords are established, pwquality must be used. |
|
|
UBTU-20-010070 |
low |
The Ubuntu operating system must prohibit password reuse for a minimum of five generations. |
|
|
UBTU-20-010072 |
low |
The Ubuntu operating system must automatically lock an account until the locked account is released by an administrator when three unsuccessful logon attempts have been made. |
|
|
UBTU-20-010074 |
medium |
The Ubuntu operating system must be configured so that the script which runs each 30 days or less to check file integrity is the default one. |
|
|
UBTU-20-010075 |
low |
The Ubuntu operating system must enforce a delay of at least 4 seconds between logon prompts following a failed logon attempt. |
|
|
UBTU-20-010100 |
medium |
The Ubuntu operating system must generate audit records for all account creations, modifications, disabling, and termination events that affect /etc/passwd. |
|
|
UBTU-20-010101 |
medium |
The Ubuntu operating system must generate audit records for all account creations, modifications, disabling, and termination events that affect /etc/group. |
|
|
UBTU-20-010102 |
medium |
The Ubuntu operating system must generate audit records for all account creations, modifications, disabling, and termination events that affect /etc/shadow. |
|
|
UBTU-20-010103 |
medium |
The Ubuntu operating system must generate audit records for all account creations, modifications, disabling, and termination events that affect /etc/gshadow. |
|
|
UBTU-20-010104 |
medium |
The Ubuntu operating system must generate audit records for all account creations, modifications, disabling, and termination events that affect /etc/opasswd. |
|
|
UBTU-20-010118 |
medium |
The Ubuntu operating system must shut down by default upon audit failure (unless availability is an overriding concern). |
|
|
UBTU-20-010122 |
medium |
The Ubuntu operating system must be configured so that audit log files are not read or write-accessible by unauthorized users. |
|
|
UBTU-20-010123 |
medium |
The Ubuntu operating system must be configured to permit only authorized users ownership of the audit log files. |
|
|
UBTU-20-010124 |
medium |
The Ubuntu operating system must permit only authorized groups ownership of the audit log files. |
|
|
UBTU-20-010128 |
medium |
The Ubuntu operating system must be configured so that the audit log directory is not write-accessible by unauthorized users. |
|
|
UBTU-20-010133 |
medium |
The Ubuntu operating system must be configured so that audit configuration files are not write-accessible by unauthorized users. |
|
|
UBTU-20-010134 |
medium |
The Ubuntu operating system must permit only authorized accounts to own the audit configuration files. |
|
|
UBTU-20-010135 |
medium |
The Ubuntu operating system must permit only authorized groups to own the audit configuration files. |
|
|
UBTU-20-010136 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the su command. |
|
|
UBTU-20-010137 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the chfn command. |
|
|
UBTU-20-010138 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the mount command. |
|
|
UBTU-20-010139 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the umount command. |
|
|
UBTU-20-010140 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the ssh-agent command. |
|
|
UBTU-20-010141 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the ssh-keysign command. |
|
|
UBTU-20-010142 |
medium |
The Ubuntu operating system must generate audit records for any use of the setxattr, fsetxattr, lsetxattr, removexattr, fremovexattr, and lremovexattr system calls. |
|
|
UBTU-20-010148 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the chown, fchown, fchownat, and lchown system calls. |
|
|
UBTU-20-010152 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the chmod, fchmod, and fchmodat system calls. |
|
|
UBTU-20-010155 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the creat, open, openat, open_by_handle_at, truncate, and ftruncate system calls. |
|
|
UBTU-20-010161 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the sudo command. |
|
|
UBTU-20-010162 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the sudoedit command. |
|
|
UBTU-20-010163 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the chsh command. |
|
|
UBTU-20-010164 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the newgrp command. |
|
|
UBTU-20-010165 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the chcon command. |
|
|
UBTU-20-010166 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the apparmor_parser command. |
|
|
UBTU-20-010167 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the setfacl command. |
|
|
UBTU-20-010168 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the chacl command. |
|
|
UBTU-20-010169 |
medium |
The Ubuntu operating system must generate audit records for the use and modification of the tallylog file. |
|
|
UBTU-20-010170 |
medium |
The Ubuntu operating system must generate audit records for the use and modification of faillog file. |
|
|
UBTU-20-010171 |
medium |
The Ubuntu operating system must generate audit records for the use and modification of the lastlog file. |
|
|
UBTU-20-010172 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the passwd command. |
|
|
UBTU-20-010173 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the unix_update command. |
|
|
UBTU-20-010174 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the gpasswd command. |
|
|
UBTU-20-010175 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the chage command. |
|
|
UBTU-20-010176 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the usermod command. |
|
|
UBTU-20-010177 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the crontab command. |
|
|
UBTU-20-010178 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the pam_timestamp_check command. |
|
|
UBTU-20-010179 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the init_module and finit_module syscalls. |
|
|
UBTU-20-010181 |
medium |
The Ubuntu operating system must generate audit records for successful/unsuccessful uses of the delete_module syscall. |
|
|
UBTU-20-010182 |
medium |
The Ubuntu operating system must produce audit records and reports containing information to establish when, where, what type, the source, and the outcome for all DoD-defined auditable events and actions in near real time. |
|
|
UBTU-20-010198 |
medium |
The Ubuntu operating system must initiate session audits at system start-up. |
|
|
UBTU-20-010199 |
medium |
The Ubuntu operating system must configure audit tools with a mode of 0755 or less permissive. |
|
|
UBTU-20-010200 |
medium |
The Ubuntu operating system must configure audit tools to be owned by root. |
|
|
UBTU-20-010201 |
medium |
The Ubuntu operating system must configure the audit tools to be group-owned by root. |
|
|
UBTU-20-010205 |
medium |
The Ubuntu operating system must use cryptographic mechanisms to protect the integrity of audit tools. |
|
|
UBTU-20-010211 |
medium |
The Ubuntu operating system must prevent all software from executing at higher privilege levels than users executing the software and the audit system must be configured to audit the execution of privileged functions. |
|
|
UBTU-20-010230 |
low |
The Ubuntu operating system must record time stamps for audit records that can be mapped to Coordinated Universal Time (UTC) or Greenwich Mean Time (GMT). |
|
|
UBTU-20-010244 |
medium |
The Ubuntu operating system must generate audit records for privileged activities, nonlocal maintenance, diagnostic sessions and other system-level access. |
|
|
UBTU-20-010267 |
medium |
The Ubuntu operating system must generate audit records for any successful/unsuccessful use of unlink, unlinkat, rename, renameat, and rmdir system calls. |
|
|
UBTU-20-010277 |
medium |
The Ubuntu operating system must generate audit records for the /var/log/wtmp file. |
|
|
UBTU-20-010278 |
medium |
The Ubuntu operating system must generate audit records for the /var/run/wtmp file. |
|
|
UBTU-20-010279 |
medium |
The Ubuntu operating system must generate audit records for the /var/log/btmp file. |
|
|
UBTU-20-010296 |
medium |
The Ubuntu operating system must generate audit records when successful/unsuccessful attempts to use modprobe command. |
|
|
UBTU-20-010297 |
medium |
The Ubuntu operating system must generate audit records when successful/unsuccessful attempts to use the kmod command. |
|
|
UBTU-20-010298 |
medium |
The Ubuntu operating system must generate audit records when successful/unsuccessful attempts to use the fdisk command. |
|
|
UBTU-20-010400 |
low |
The Ubuntu operating system must limit the number of concurrent sessions to ten for all accounts and/or account types. |
|
|
UBTU-20-010403 |
medium |
The Ubuntu operating system must monitor remote access methods. |
|
|
UBTU-20-010404 |
medium |
The Ubuntu operating system must encrypt all stored passwords with a FIPS 140-2 approved cryptographic hashing algorithm. |
|
|
UBTU-20-010405 |
high |
The Ubuntu operating system must not have the telnet package installed. |
|
|
UBTU-20-010406 |
high |
The Ubuntu operating system must not have the rsh-server package installed. |
|
|
UBTU-20-010407 |
medium |
The Ubuntu operating system must be configured to prohibit or restrict the use of functions, ports, protocols, and/or services, as defined in the PPSM CAL and vulnerability assessments. |
|
|
UBTU-20-010408 |
medium |
The Ubuntu operating system must prevent direct login into the root account. |
|
|
UBTU-20-010411 |
medium |
The Ubuntu operating system must set a sticky bit on all public directories to prevent unauthorized and unintended information transferred via shared system resources. |
|
|
UBTU-20-010412 |
medium |
The Ubuntu operating system must be configured to use TCP syncookies. |
|
|
UBTU-20-010413 |
medium |
The Ubuntu operating system must disable kernel core dumps so that it can fail to a secure state if system initialization fails, shutdown fails or aborts fail. |
|
|
UBTU-20-010416 |
medium |
The Ubuntu operating system must generate error messages that provide information necessary for corrective actions without revealing information that could be exploited by adversaries. |
|
|
UBTU-20-010417 |
medium |
The Ubuntu operating system must configure the /var/log directory to be group-owned by syslog. |
|
|
UBTU-20-010418 |
medium |
The Ubuntu operating system must configure the /var/log directory to be owned by root. |
|
|
UBTU-20-010419 |
medium |
The Ubuntu operating system must configure the /var/log directory to have mode 0750 or less permissive. |
|
|
UBTU-20-010420 |
medium |
The Ubuntu operating system must configure the /var/log/syslog file to be group-owned by adm. |
Logs of processes running with reduced permissions are in /tmp/VeeamBackup because of this |
|
UBTU-20-010421 |
medium |
The Ubuntu operating system must configure /var/log/syslog file to be owned by syslog. |
|
|
UBTU-20-010422 |
medium |
The Ubuntu operating system must configure /var/log/syslog file with mode 0640 or less permissive. |
|
|
UBTU-20-010423 |
medium |
The Ubuntu operating system must have directories that contain system commands set to a mode of 0755 or less permissive. |
|
|
UBTU-20-010424 |
medium |
The Ubuntu operating system must have directories that contain system commands owned by root. |
|
|
UBTU-20-010425 |
medium |
The Ubuntu operating system must have directories that contain system commands group-owned by root. |
|
|
UBTU-20-010426 |
medium |
The Ubuntu operating system library files must have mode 0755 or less permissive. |
|
|
UBTU-20-010427 |
medium |
The Ubuntu operating system library directories must have mode 0755 or less permissive. |
|
|
UBTU-20-010428 |
medium |
The Ubuntu operating system library files must be owned by root. |
|
|
UBTU-20-010429 |
medium |
The Ubuntu operating system library directories must be owned by root. |
|
|
UBTU-20-010430 |
medium |
The Ubuntu operating system library files must be group-owned by root or a system account. |
|
|
UBTU-20-010431 |
medium |
The Ubuntu operating system library directories must be group-owned by root. |
|
|
UBTU-20-010432 |
medium |
The Ubuntu operating system must be configured to preserve log records from failure events. |
|
|
UBTU-20-010433 |
medium |
The Ubuntu operating system must have an application firewall installed in order to control remote access methods. |
|
|
UBTU-20-010434 |
medium |
The Ubuntu operating system must enable and run the uncomplicated firewall(ufw). |
|
|
UBTU-20-010435 |
medium |
The Ubuntu operating system must, for networked systems, compare internal information system clocks at least every 24 hours with a server which is synchronized to one of the redundant United States Naval Observatory (USNO) time servers, or a time server designated for the appropriate DoD network (NIPRNet/SIPRNet), and/or the Global Positioning System (GPS). |
The script sets the “-R” flag in /etc/defaults/chrony
That prevents chrony from making big time changes during boot or restart of the service. See this blog post for details.
|
|
UBTU-20-010438 |
medium |
The Ubuntu operating system’s Advance Package Tool (APT) must be configured to prevent the installation of patches, service packs, device drivers, or Ubuntu operating system components without verification they have been digitally signed using a certificate that is recognized and approved by the organization. |
|
|
UBTU-20-010439 |
medium |
The Ubuntu operating system must be configured to use AppArmor. |
|
|
UBTU-20-010446 |
medium |
The Ubuntu operating system must configure the uncomplicated firewall to rate-limit impacted network interfaces. |
|
|
UBTU-20-010448 |
medium |
The Ubuntu operating system must implement address space layout randomization to protect its memory from unauthorized code execution. |
|
|
UBTU-20-010449 |
medium |
The Ubuntu operating system must be configured so that Advance Package Tool (APT) removes all software components after updated versions have been installed. |
|
|
UBTU-20-010450 |
medium |
The Ubuntu operating system must use a file integrity tool to verify correct operation of all security functions. |
|
|
UBTU-20-010451 |
medium |
The Ubuntu operating system must notify designated personnel if baseline configurations are changed in an unauthorized manner. The file integrity tool must notify the System Administrator when changes to the baseline configuration or anomalies in the operation of any security functions are discovered. |
|
|
UBTU-20-010453 |
low |
The Ubuntu operating system must display the date and time of the last successful account logon upon logon. |
|
|
UBTU-20-010454 |
medium |
The Ubuntu operating system must have an application firewall enabled. |
|
|
UBTU-20-010456 |
medium |
The Ubuntu operating system must have system commands set to a mode of 0755 or less permissive. |
|
|
UBTU-20-010457 |
medium |
The Ubuntu operating system must have system commands owned by root or a system account. |
|
|
UBTU-20-010458 |
medium |
The Ubuntu operating system must have system commands group-owned by root or a system account. |
|
|
UBTU-20-010460 |
high |
The Ubuntu operating system must disable the x86 Ctrl-Alt-Delete key sequence. |
|
|
UBTU-20-010462 |
high |
The Ubuntu operating system must not have accounts configured with blank or null passwords. |
|
|
UBTU-20-010463 |
high |
The Ubuntu operating system must not allow accounts configured with blank or null passwords. |
|
|
UBTU-20-010461 |
medium |
The Ubuntu operating system must disable automatic mounting of Universal Serial Bus (USB) mass storage driver. |
The table below shows the DISA STIG requirements that are not applicable. Many of them are out of scope because there is only one (locked down) user account, no graphical user interface and this guide does not require having a mail server set up for notifications. FIPS compliance can also only be achieved by using Ubuntu Pro, while this guide refers to the free version.
| STIG ID | Severity | Rule Title | Comment |
| UBTU-20-010000 | medium | The Ubuntu operating system must provision temporary user accounts with an expiration time of 72 hours or less. | There are no temporary accounts. |
|
UBTU-20-010002 |
medium |
The Ubuntu operating system must enable the graphical user logon banner to display the Standard Mandatory DoD Notice and Consent Banner before granting local access to the system via a graphical user logon. |
No GUI installed |
|
UBTU-20-010003 |
medium |
The Ubuntu operating system must display the Standard Mandatory DoD Notice and Consent Banner before granting local access to the system via a graphical user logon. |
No GUI installed |
|
UBTU-20-010004 |
medium |
The Ubuntu operating system must retain a user’s session lock until that user re-establishes access using established identification and authentication procedures. |
No GUI installed |
|
UBTU-20-010006 |
high |
The Ubuntu operating system must map the authenticated identity to the user or group account for PKI-based authentication. |
Only one (locked down) user on the system. |
|
UBTU-20-010010 |
medium |
The Ubuntu operating system must uniquely identify interactive users. |
There are no interactive users |
|
UBTU-20-010033 |
medium |
The Ubuntu operating system must implement smart card logins for multifactor authentication for local and network access to privileged and non-privileged accounts. |
There are no interactive users |
|
UBTU-20-010044 |
medium |
The Ubuntu operating system must configure the SSH daemon to use FIPS 140-2 approved ciphers to prevent the unauthorized disclosure of information and/or detect changes to information during transmission. |
SSH is disabled |
|
UBTU-20-010060 |
medium |
The Ubuntu operating system, for PKI-based authentication, must validate certificates by constructing a certification path (which includes status information) to an accepted trust anchor. |
There are no interactive users |
|
UBTU-20-010063 |
medium |
The Ubuntu operating system must implement multifactor authentication for remote access to privileged accounts in such a way that one of the factors is provided by a device separate from the system gaining access. |
There is no remote access to privileged accounts |
|
UBTU-20-010064 |
medium |
The Ubuntu operating system must accept Personal Identity Verification (PIV) credentials. |
There are no interactive users and no smart cards |
|
UBTU-20-010065 |
medium |
The Ubuntu operating system must electronically verify Personal Identity Verification (PIV) credentials. |
There are no interactive users and no smart cards |
|
UBTU-20-010066 |
medium |
The Ubuntu operating system for PKI-based authentication, must implement a local cache of revocation data in case of the inability to access revocation information via the network. |
There are no interactive users and no smart cards |
|
UBTU-20-010117 |
medium |
The Ubuntu operating system must alert the ISSO and SA (at a minimum) in the event of an audit processing failure. |
This guide does not require 3rd party services for notifications |
|
UBTU-20-010215 |
low |
The Ubuntu operating system must allocate audit record storage capacity to store at least one weeks’ worth of audit records, when audit records are not immediately sent to a central audit record storage facility. |
Setting up configuration for audit storage 5GB are for /var/log/audit – as there should be almost nothing in the logs, this should be more than enough We just use percentage value, we don’t have knowledge about customer audit volume. |
|
UBTU-20-010216 |
low |
The Ubuntu operating system audit event multiplexor must be configured to off-load audit logs onto a different system or storage media from the system being audited. |
This guide does not require 3rd party services for notifications |
|
UBTU-20-010217 |
low |
The Ubuntu operating system must immediately notify the SA and ISSO (at a minimum) when allocated audit record storage volume reaches 75% of the repository maximum audit record storage capacity. |
This guide does not require 3rd party services for notifications |
|
UBTU-20-010300 |
low |
The Ubuntu operating system must have a crontab script running weekly to offload audit events of standalone systems. |
This guide does not require 3rd party services for notifications |
|
UBTU-20-010409 |
medium |
The Ubuntu operating system must disable account identifiers (individuals, groups, roles, and devices) after 35 days of inactivity. |
There is only one (locked down) account |
|
UBTU-20-010410 |
low |
The Ubuntu operating system must automatically remove or disable emergency accounts after 72 hours. |
There is only one (locked down) account |
|
UBTU-20-010415 |
low |
The Ubuntu operating system must deploy Endpoint Security for Linux Threat Prevention (ENSLTP). |
This guide does not require 3rd party products |
|
UBTU-20-010436 |
low |
The Ubuntu operating system must synchronize internal information system clocks to the authoritative time source when the time difference is greater than one second. |
See UBTU-20-010435. The assumption is, that an attacker could manipulate the NTP servers or network communication |
|
UBTU-20-010437 |
medium |
The Ubuntu operating system must notify designated personnel if baseline configurations are changed in an unauthorized manner. The file integrity tool must notify the System Administrator when changes to the baseline configuration or anomalies in the oper |
Default system settings
We have no mail server configured |
|
UBTU-20-010440 |
medium |
The Ubuntu operating system must allow the use of a temporary password for system logons with an immediate change to a permanent password. |
There is only one (locked down) account |
|
UBTU-20-010441 |
low |
The Ubuntu operating system must be configured such that Pluggable Authentication Module (PAM) prohibits the use of cached authentications after one day. |
There are no cached credentials |
|
UBTU-20-010442 |
high |
The Ubuntu operating system must implement NIST FIPS-validated cryptography to protect classified information and for the following: to provision digital signatures, to generate cryptographic hashes, and to protect unclassified information requiring confidentiality and cryptographic protection in accordance with applicable federal laws, Executive Orders, directives, policies, regulations, and standards. |
Only Ubuntu Pro has that |
|
UBTU-20-010443 |
medium |
The Ubuntu operating system must only allow the use of DoD PKI-established certificate authorities for verification of the establishment of protected sessions. |
There is only one (locked down) account |
|
UBTU-20-010459 |
high |
The Ubuntu operating system must disable the x86 Ctrl-Alt-Delete key sequence if a graphical user interface is installed. |
No GUI installed. |
The post Securing Veeam Hardened Repository appeared first on Veeam Software Official Blog.
Original post here: Securing Veeam Hardened Repository
- Get link
- X
- Other Apps


Comments
Post a Comment